Ubuntu can be configured to provide remote access to the graphical desktop environment over a network or internet connection. Although not enabled by default, it is relatively straightforward to display and access an Ubuntu desktop from a system anywhere else on a network or the internet. This can be achieved regardless of whether that system is running Linux, Windows, or macOS. In fact, there are even apps available for Android and iOS that will allow you to access your Ubuntu desktop from just about anywhere that a data signal is available.
Remote desktop access can be useful in a number of scenarios. It enables you or another person, for example, to view and interact with your Ubuntu desktop environment from another computer system either on the same network or over the internet. This is useful if you need to work on your computer when you are away from your desk, such as while traveling. It is also useful in situations where a co-worker or IT support technician needs access to your desktop to resolve a problem.
The Ubuntu remote desktop supports connections using either Virtual Network Computing (VNC) or Microsoft’s Remote Desktop Protocol (RDP). An advantage of using RDP is that it makes the Ubuntu desktop easily accessible from Windows clients. In this chapter, therefore, we will cover the key aspects of configuring and using remote desktops within Ubuntu using RDP.
Remote Desktop Access Types
Before starting, it is important to understand that there are essentially two types of remote desktop access. The approach covered in this chapter is useful if you primarily use Ubuntu as a desktop operating system and require remote access to your usual desktop session. When configured, you will take over your desktop session and view and control it remotely.
The second option is intended for situations where you need to start and access one or more remote desktop sessions on a remote server-based system, regardless of whether the remote system has a graphical console attached. This allows you to launch multiple desktop sessions in the background on the remote system and view and control those desktops over a network or internet connection.
 |
You are reading a sample chapter from Ubuntu 22.04 Essentials. Buy the full book now in eBook ($24.99) format. Includes 36 chapters. Learn more. |
Secure and Insecure Remote Desktop Access
In this chapter, we will cover both secure and insecure remote desktop access methods. Assuming that you are accessing one system from another within the context of a secure internal network, then it is generally safe to use the insecure access method. If, on the other hand, you plan to access your desktop remotely over any kind of public network, you must use the secure method of access to avoid your system and data being compromised.
Enabling Remote Desktop Access on Ubuntu
Remote desktop access on Ubuntu is provided by the Vino package. Vino is a remote desktop server that was developed specifically for use with the GNOME desktop. The first step in enabling remote access is to install this package:
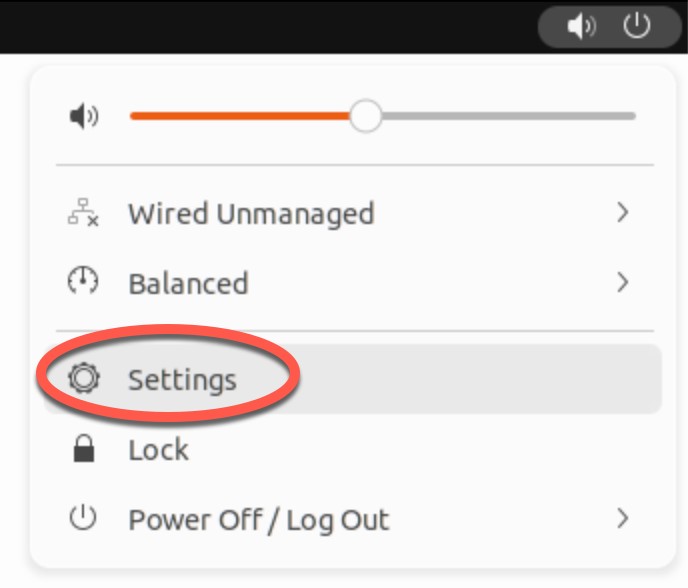
# apt install vinoCode language: plaintext (plaintext)Once Vino has been installed, the next step is to enable remote desktop access from within GNOME. Begin by opening the settings app as shown in Figure 18-1:
From within the Settings application, select the Sharing option (marked A in Figure 18-2):
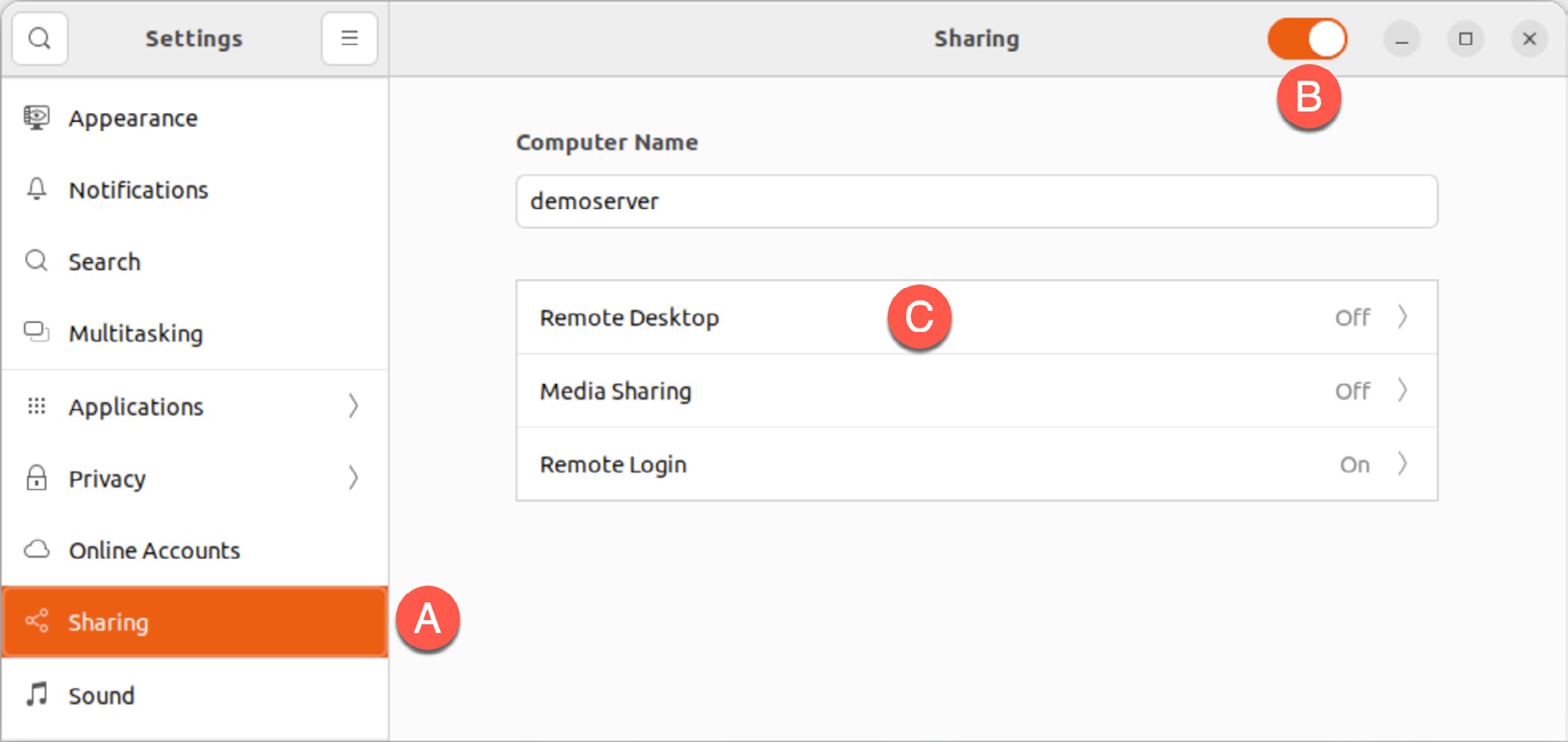
Turn on the Sharing switch (B) and click on the Remote Desktop option (C) to display the dialog shown in Figure 18-3 below:
 |
You are reading a sample chapter from Ubuntu 22.04 Essentials. Buy the full book now in eBook ($24.99) format. Includes 36 chapters. Learn more. |
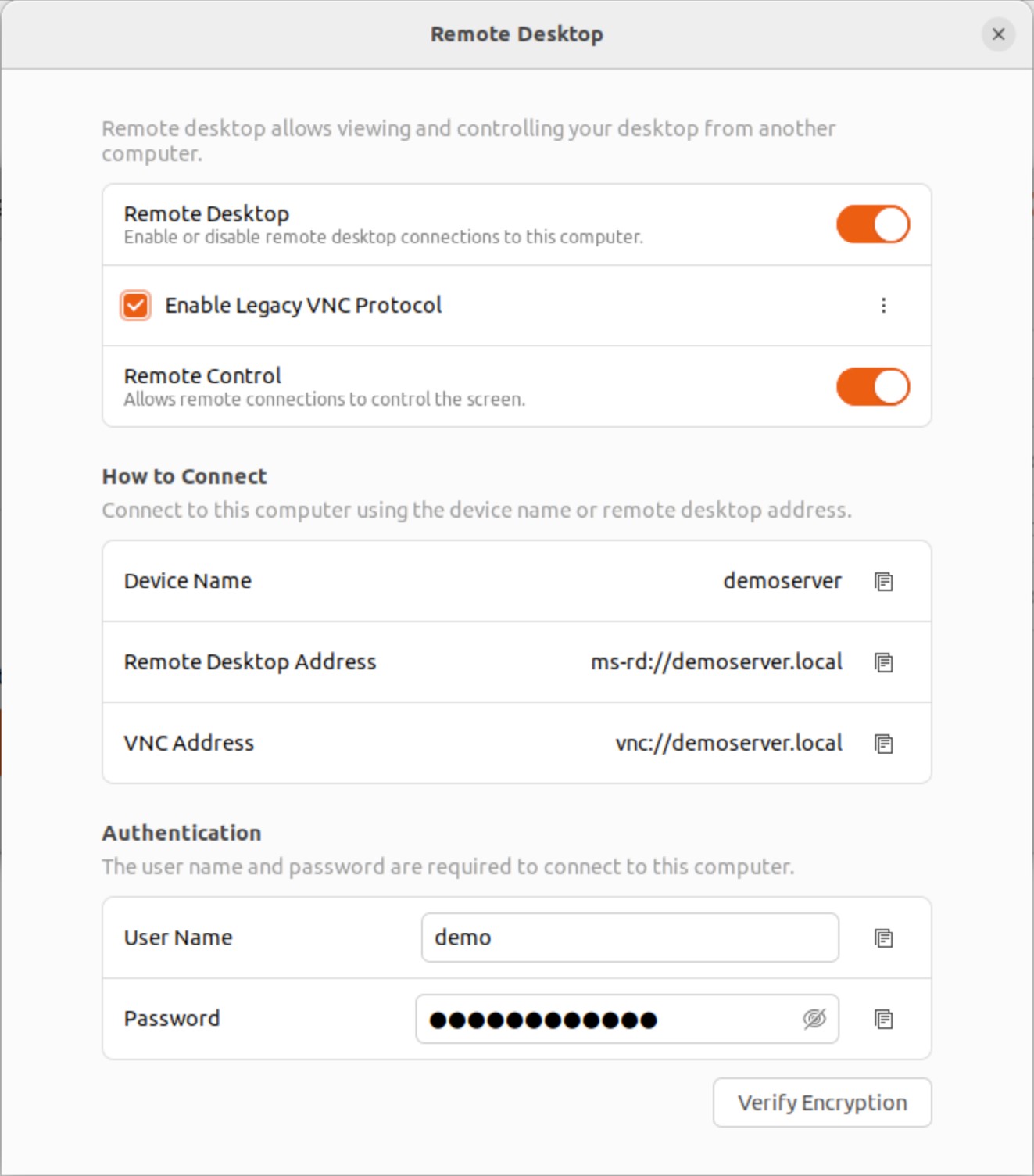
The Remote Desktop dialog provides the following configuration options to manage remote desktop access:
- Remote Control – If enabled, the remote session will be able to use the mouse and keyboard to interact with the desktop environment. If this option disabled, the remote session will only allow the desktop to be viewed.
- Enable Legacy VNC Protocol – Ubuntu supports remote desktop via VNC and Microsoft’s Remote Desktop Protocol (RDP). When enabled, two additional options are available within the menu shown in Figure 18-4 below:
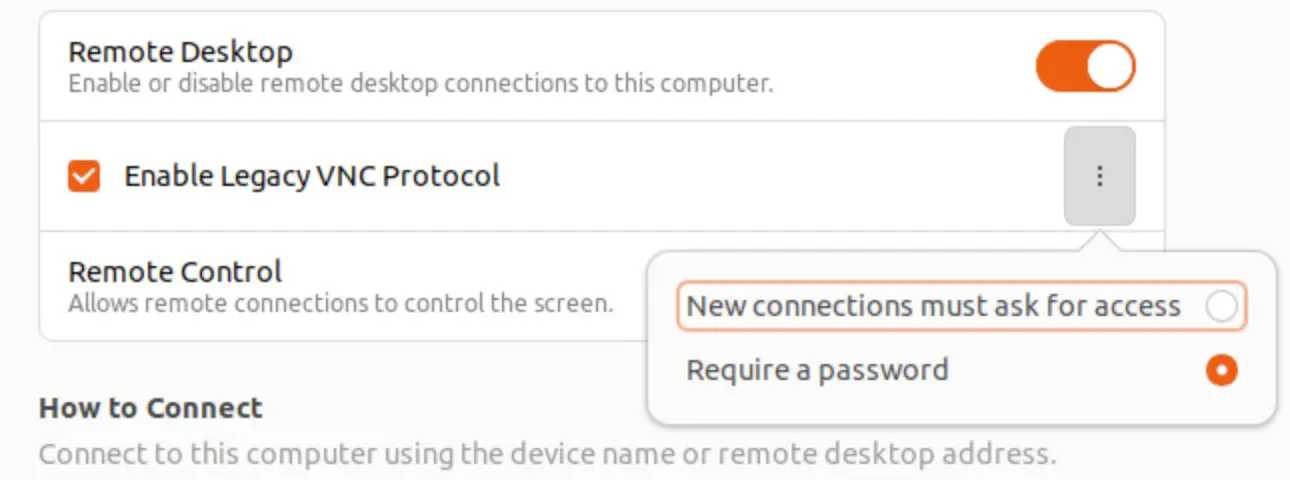
- New connections must ask for access – When selected, a prompt will appear on the host screen asking to give permission to the remote user to access the desktop. Do not select this option if you plan to access your screen remotely and nobody will be at the host system to accept the connection request.
- Require a password – Requires the user to enter the specified password prior to gaining access to the desktop.
- User Name and Password – The user name and password that will be required to remotely access the desktop. After configuring the settings, close both the Remote Desktop and Settings dialogs.
Connecting to the Shared Desktop
Although Remote Desktop viewer implementations are available for a wide range of operating systems, a tool such as the Remmina Desktop Client is recommended when connecting from Ubuntu or other Linux-based systems. Remmina is a user-friendly tool with a graphical interface that supports the encryption used by Vino to ensure a secure remote connection.
Remmina is usually installed by default on Ubuntu but can be installed if necessary as follows:
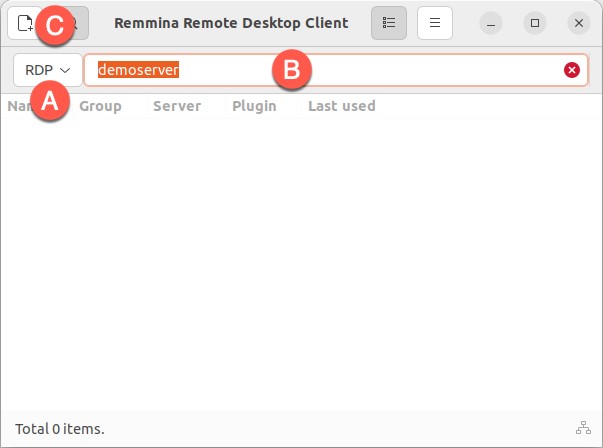
# apt install remminaCode language: plaintext (plaintext)Launch Remmina on the remote Linux computer and change the connection type menu (marked A in Figure 18-5) to RDP, and enter into the address field (B) the IP address or hostname of the remote system to which you wish to connect (you can also create a connection and save it using the button marked C):
To establish the connection, tap the keyboard Enter key to begin the connection process. Click to accept the certificate, after which a second screen will appear requesting the desktop access password:
 |
You are reading a sample chapter from Ubuntu 22.04 Essentials. Buy the full book now in eBook ($24.99) format. Includes 36 chapters. Learn more. |
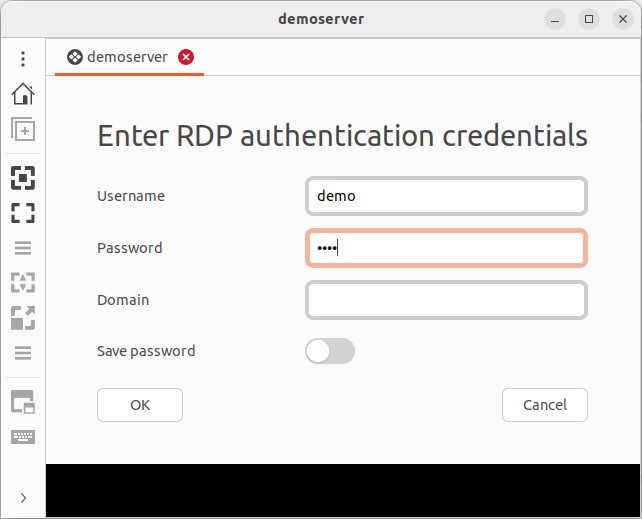
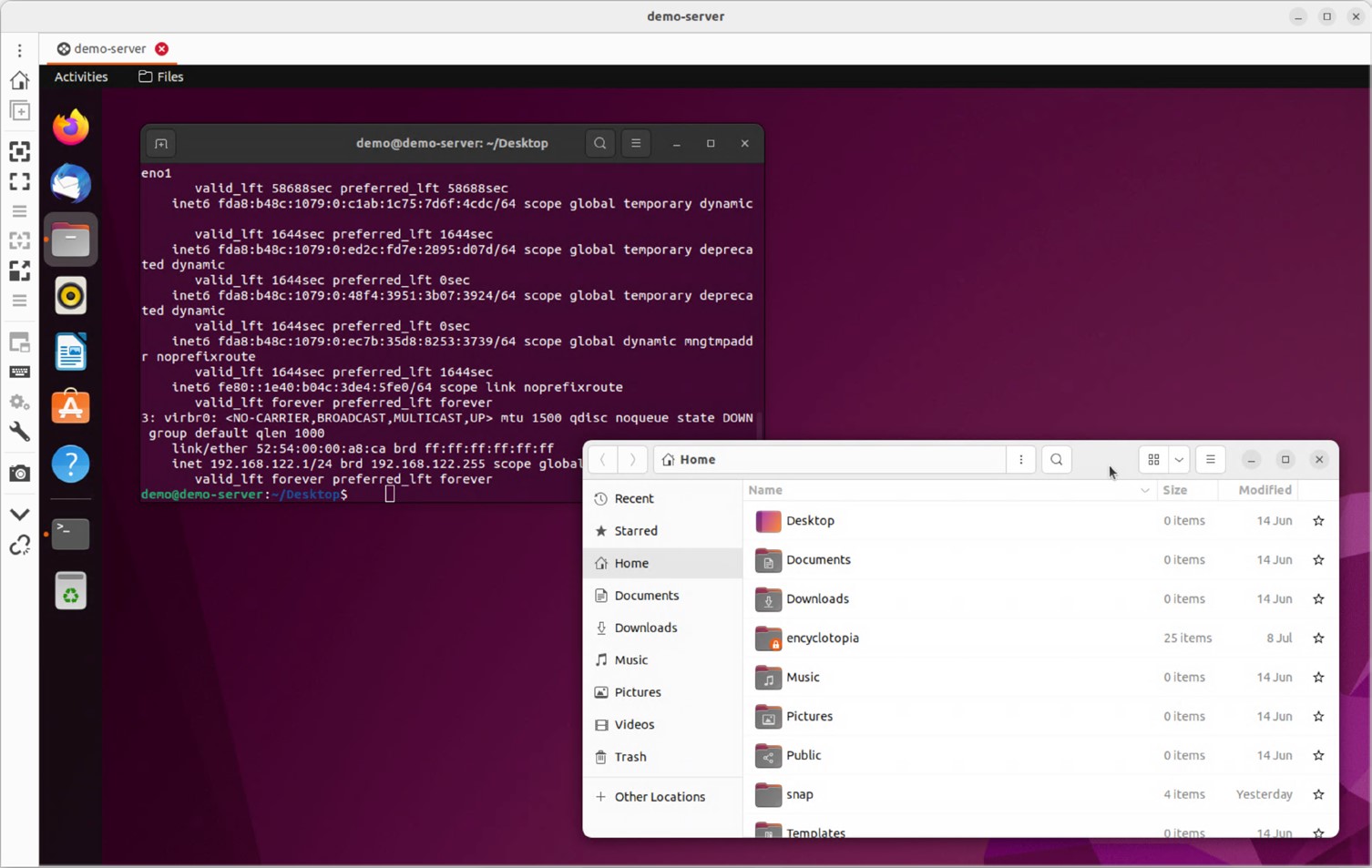
After entering the password, click on OK to access the remote screen:
Connecting from Windows
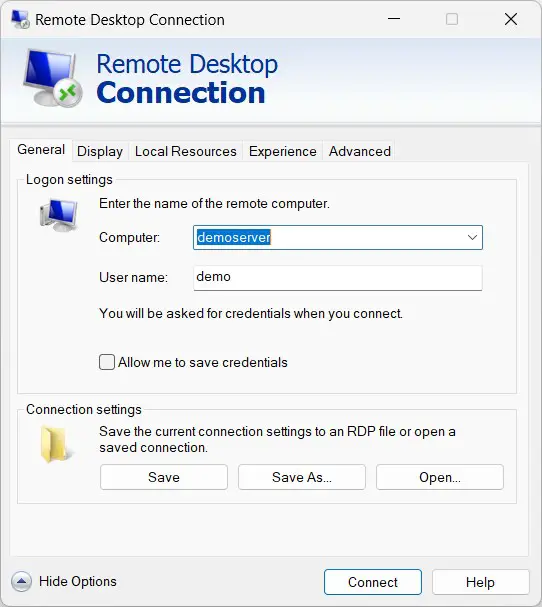
Because we have configured Vino to use RDP, the Ubuntu desktop is also accessible from Windows clients using Microsoft’s Remote Desktop Connection application. On a Windows system, start Remote Desktop Connection and click on the Show Options button in the bottom right-hand corner to display additional configuration settings. Enter the hostname or IP address of the Ubuntu system and the user name that was configured earlier in the chapter:
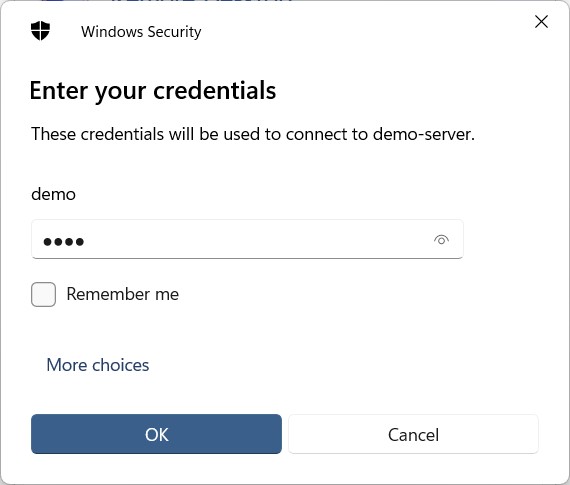
Click the connect button and, when prompted, enter the password to gain access to the Ubuntu desktop:
Summary
Remote access to the GNOME desktop environment of an Ubuntu system can be enabled by making use of Virtual Network Computing (VNC) or the Remote Desktop Protocol (RDP). Comprising the server running on the remote server and a corresponding client on the local host, VNC and RDP allow remote access to desktop instances running on the server.
The standard remote server solution for the GNOME desktop is Vino. Once installed, remote desktop sessions can be established from other Linux systems using a remote desktop viewer such as Remmina. When using RDP, the desktop is also accessible to Windows and Mac systems using the Microsoft Remote Desktop Connection application.
 |
You are reading a sample chapter from Ubuntu 22.04 Essentials. Buy the full book now in eBook ($24.99) format. Includes 36 chapters. Learn more. |