A firewall is vital in protecting a computer system or network of computers from external attack (typically from an external source via an internet connection). For example, any computer connected directly to an internet connection must run a firewall to protect against malicious activity. Similarly, any internal network must have some form of firewall between it and an external internet connection.
All Linux distributions are provided with a firewall solution of some form. In the case of RHEL 9, this takes the form of a service named firewalld.
While firewall configuration can be complex, RHEL 9 provides command-line, web-based, and graphical tools that ease the firewall configuration process. This chapter will introduce the basic concepts of firewalld and cover the steps necessary to configure a firewall using the tools provided with the operating system.
An Introduction to firewalld
The firewalld service uses a set of rules to control incoming network traffic and define which traffic is to be blocked and which is to be allowed to pass through to the system and is built on top of a more complex firewall tool named iptables.
The firewalld system provides a flexible way to manage incoming traffic. The firewall could, for example, be configured to block traffic from a specific external IP address or prevent traffic from arriving on a particular TCP/IP port. Rules may also be defined to forward incoming traffic to different systems or to act as an internet gateway to protect other computers on a network.
 |
You are reading a sample chapter from Red Hat Enterprise Linux 9 Essentials. Buy the full book now in eBook or Print format.
Includes 34 chapters and 290 pages. Learn more. |
In keeping with standard security practices, a default firewalld installation is configured to block all access except SSH remote login and the DHCP service used by the system to obtain a dynamic IP address (both of which are essential if the system administrator is to be able to gain access to the system after completing the installation).
The critical elements of firewall configuration on RHEL 9 are zones, interfaces, services, and ports.
Zones
By default, firewalld is installed with a range of pre-configured zones. A zone is a preconfigured set of rules that can be applied to the system at any time to implement firewall configurations for specific scenarios quickly. The block zone, for example, blocks all incoming traffic, while the home zone imposes less strict rules on the assumption that the system is running in a safer environment where a greater level of trust is expected. New zones may be added to the system, and existing zones modified to add or remove rules. Zones may also be deleted entirely from the system. Table 14-1 lists the set of zones available by default on a RHEL 9 system:
|
Zone |
Description |
|
drop | The most secure zone. Only outgoing connections are permitted, and all incoming connections are dropped without any notification to the connecting client. |
|
block | Similar to the drop zone, with the exception that incoming connections are rejected with an icmp-host-prohibited or icmp6-adm-prohibited notification. |
|
public |
Intended for use when connected to public networks or the internet where other computers are not known to be trustworthy. Allows select incoming connections. |
|
external | When a system acts as the internet gateway for a network of computers, the external zone is applied to the interface connected to the internet. This zone is used with the internal zone when implementing masquerading or network address translation (NAT), as outlined later in this chapter. Allows select incoming connections |
|
internal | Used with the external zone and applied to the interface connected to the internal network. Assumes that the computers on the internal network are trusted. Allows select incoming connections. |
|
dmz |
For use when the system is running in the demilitarized zone (DMZ). These are generally computers that are publicly accessible but isolated from other parts of your internal network. Allows select incoming connections. |
|
work |
For use when running a system on a network in a work environment where other computers are trusted. Allows select incoming connections. |
|
home |
For use when running a system on a home network where other computers are trusted. Allows select incoming connections. |
|
trusted |
The least secure zone. All incoming connections are accepted. |
| nm-shared | This zone is used internally by NetworkManager when implementing connection sharing. |
| libvirt | Used by virtual networks, typically when the host is running virtual machines. |
To review specific settings for a zone, refer to the corresponding XML configuration file located on the system in the /usr/lib/firewalld/zones directory. The following, for example, lists the content of the public.xml zone configuration file:
<?xml version="1.0" encoding="utf-8"?> <zone> <short>Public</short> <description>For use in public areas. You do not trust the other computers on networks to not harm your computer. Only selected incoming connections are accepted.</description> <service name="ssh"/> <service name="dhcpv6-client"/> <service name="cockpit"/> <forward/> </zone>
Interfaces
Any RHEL 9 system connected to the internet or a network (or both) will contain at least one interface in the form of either a physical or virtual network device. When firewalld is active, each of these interfaces is assigned to a zone allowing different levels of firewall security to be assigned to different interfaces. For example, consider a server containing two interfaces; one connected externally to the internet and the other to an internal network. In such a scenario, the external facing interface would most likely be assigned to the more restrictive external zone, while the internal interface might use the internal zone.
 |
You are reading a sample chapter from Red Hat Enterprise Linux 9 Essentials. Buy the full book now in eBook or Print format.
Includes 34 chapters and 290 pages. Learn more. |
Services
TCP/IP defines a set of services that communicate on standard ports. Secure HTTPS web connections, for example, use port 443, while the SMTP email service uses port 25. To selectively enable incoming traffic for specific services, firewalld rules can be added to zones. The home zone, for example, does not permit incoming HTTPS connections by default. This traffic can be enabled by adding rules to a zone to allow incoming HTTPS connections without having to reference the specific port number.
Ports
Although common TCP/IP services can be referenced when adding firewalld rules, situations will arise where incoming connections need to be allowed on a specific port that is not allocated to a service. This can be achieved by adding rules referencing specific ports instead of services. This technique was used in the chapter An Overview of the RHEL 9 Cockpit Web Interface when port 9090 was opened to allow access to the Cockpit web interface.
Checking firewalld Status
The firewalld service is installed and enabled by default on all RHEL 9 installations. The status of the service can be checked via the following command:
# systemctl status firewalld
firewalld.service - firewalld - dynamic firewall daemon
Loaded: loaded (/usr/lib/systemd/system/firewalld.service; enabled; vendor preset: enabled)
Active: active (running) since Thu 2019-02-14 14:24:31 EST; 3 days ago
Docs: man:firewalld(1)
Main PID: 816 (firewalld)
Tasks: 2 (limit: 25026)
Memory: 30.6M
CGroup: /system.slice/firewalld.service
816 /usr/libexec/platform-python -s /usr/sbin/firewalld --nofork --nopidIf necessary, the firewalld service may be installed as follows:
# dnf install firewalld
The firewalld service is enabled by default and will start automatically after installation and each time the system boots.
 |
You are reading a sample chapter from Red Hat Enterprise Linux 9 Essentials. Buy the full book now in eBook or Print format.
Includes 34 chapters and 290 pages. Learn more. |
Configuring Firewall Rules with firewall-cmd
The firewall-cmd command-line utility allows information about the firewalld configuration to be viewed and changes to be made to zones and rules from within a terminal window.
When making changes to the firewall settings, it is important to be aware of the concepts of runtime and permanent configurations. By default, any rule changes are considered to be runtime configuration changes. This means that while the changes will take effect immediately, they will be lost next time the system restarts or the firewalld service reloads, for example, by issuing the following command:
# firewall-cmd --reload
The –permanent command-line option must be used to make a change permanent. Permanent changes do not occur until the firewalld service reloads but will remain in place until manually changed.
Identifying and Changing the Default Zone
To identify the default zone (in other words, the zone to which all interfaces will be assigned unless a different zone is specifically selected), use the firewall-cmd tool as follows:
# firewall-cmd --get-default-zone public
To change the default to a different zone:
 |
You are reading a sample chapter from Red Hat Enterprise Linux 9 Essentials. Buy the full book now in eBook or Print format.
Includes 34 chapters and 290 pages. Learn more. |
# firewall-cmd --set-default-zone=home success
Displaying Zone Information
To list all of the zones available on the system:
# firewall-cmd --get-zones block dmz drop external home internal libvirt nm-shared public trusted work
Obtain a list of zones currently active together with the interfaces to which they are assigned as follows:
# firewall-cmd --get-active-zones external interfaces: eth0 internal interfaces: eth1
All of the rules currently configured for a specific zone may be listed as follows:
# firewall-cmd --zone=home --list-all home (active) target: default icmp-block-inversion: no interfaces: eth0 sources: services: cockpit dhcpv6-client mdns samba-client ssh ports: protocols: masquerade: no forward-ports: source-ports: icmp-blocks: rich rules:
Use the following command to list the services currently available for inclusion in a firewalld rule:
# firewall-cmd --get-services RH-Satellite-6 amanda-client amanda-k5-client amqp amqps apcupsd audit bacula bacula-client bgp bitcoin bitcoin-rpc bitcoin-testnet bitcoin-testnet-rpc ceph ceph-mon cfengine cockpit ...
To list the services currently enabled for a zone:
 |
You are reading a sample chapter from Red Hat Enterprise Linux 9 Essentials. Buy the full book now in eBook or Print format.
Includes 34 chapters and 290 pages. Learn more. |
# firewall-cmd --zone=public --list-services cockpit dhcpv6-client ssh
A list of port rules can be obtained as follows:
# firewall-cmd --zone=public --list-ports 9090/tcp
Adding and Removing Zone Services
To add a service to a zone, in this case, adding HTTPS to the public zone, the following command would be used:
# firewall-cmd --zone=public --add-service=https success
By default, this is a runtime change, so the added rule will be lost after a system reboot. To add a service permanently so that it remains in effect next time the system restarts, use the –permanent flag:
# firewall-cmd --zone=public --permanent --add-service=https success
To verify that a service has been added permanently, be sure to include the –permanent flag when requesting the service list:
# firewall-cmd --zone=public --permanent --list-services cockpit dhcpv6-client http https ssh
Note that as a permanent change, this new rule will not take effect until the system restarts or firewalld reloads:
 |
You are reading a sample chapter from Red Hat Enterprise Linux 9 Essentials. Buy the full book now in eBook or Print format.
Includes 34 chapters and 290 pages. Learn more. |
# firewall-cmd --reload
Remove a service from a zone using the –remove-service option. Since this is a runtime change, the rule will be re-instated the next time the system restarts:
# firewall-cmd --zone=public --remove-service=https
To remove a service permanently, use the –permanent flag, remembering to reload firewalld if the change is required to take immediate effect:
# firewall-cmd --zone=public --permanent --remove-service=https
Working with Port-based Rules
To enable a specific port, use the –add-port option. Note that when manually defining the port, both the port number and protocol (TCP or UDP) will need to be provided:
# firewall-cmd --zone=public --permanent --add-port=5000/tcp
It is also possible to specify a range of ports when adding a rule to a zone:
# firewall-cmd --zone=public --permanent --add-port=5900-5999/udp
Creating a New Zone
An entirely new zone may be created by running the following command. Once created, the zone may be managed in the same way as any of the predefined zones:
 |
You are reading a sample chapter from Red Hat Enterprise Linux 9 Essentials. Buy the full book now in eBook or Print format.
Includes 34 chapters and 290 pages. Learn more. |
# firewall-cmd --permanent --new-zone=myoffice success
After adding a new zone, firewalld will need to be restarted before the zone becomes available:
# firewall-cmd --reload success
Changing Zone/Interface Assignments
As previously discussed, each interface on the system must be assigned to a zone. The zone to which an interface is assigned can also be changed using the firewall-cmd tool. In the following example, the eth0 interface is assigned to the public zone:
# firewall-cmd --zone=public --change-interface=eth0 success
Masquerading
Masquerading is better known in networking administration circles as Network Address Translation (NAT). For example, when using a RHEL 9 system as a gateway to the internet for a network of computers, masquerading allows all of the internal systems to use the IP address of that RHEL 9 system when communicating over the internet. This has the advantage of hiding the internal IP addresses of any systems from malicious external entities and also avoids the necessity to allocate a public IP address to every computer on the network.
Use the following command to check whether masquerading is already enabled on the firewall:
# firewall-cmd --zone=external --query-masquerade
Use the following command to enable masquerading (remembering to use the –permanent flag if the change is to be permanent):
 |
You are reading a sample chapter from Red Hat Enterprise Linux 9 Essentials. Buy the full book now in eBook or Print format.
Includes 34 chapters and 290 pages. Learn more. |
# firewall-cmd --zone=external --add-masquerade
Adding ICMP Rules
Client systems use the Internet Control Message Protocol (ICMP) on networks to send information, such as error messages, to each other. It is also the foundation of the ping command, which is used by network administrators and users alike to detect whether a particular client is alive on a network. The ICMP category allows for the blocking of specific ICMP message types. For example, an administrator might choose to block incoming ping (Echo Request) ICMP messages to prevent the possibility of a ping-based denial of service (DoS) attack (where a server is maliciously bombarded with so many ping messages that it becomes unable to respond to legitimate requests).
To view the ICMP types available for inclusion in firewalld rules, run the following command:
# firewall-cmd --get-icmptypes address-unreachable bad-header beyond-scope communication-prohibited destinationunreachable echo-reply ...
The following command, for example, permanently adds a rule to block echo-reply (ping request) messages for the public zone:
# firewall-cmd --zone=public --permanent --add-icmp-block=echo-reply
Implementing Port Forwarding
Port forwarding is used in conjunction with masquerading when the RHEL 9 system acts as a gateway to the internet for an internal network of computer systems. Port forwarding allows traffic arriving at the firewall via the internet on a specific port to be forwarded to a particular system on the internal network. This is perhaps best described by way of an example.
Suppose that a RHEL 9 system is acting as the firewall for an internal network of computers, and one of the systems on the network is configured as a web server. Let’s assume the web server system has an IP address of 192.168.2.20. The domain record for the website hosted on this system is configured with the public IP address behind which the RHEL 9 firewall system sits. When an HTTP web page request arrives on port 80, the RHEL 9 system acting as the firewall needs to know what to do with it. By configuring port forwarding, it is possible to direct all web traffic to the internal system hosting the web server (in this case, IP address 192.168.2.20), either continuing to use port 80 or diverting the traffic to a different port on the destination server. Port forwarding can even be configured to forward the traffic to a different port on the same system as the firewall (a concept known as local forwarding).
 |
You are reading a sample chapter from Red Hat Enterprise Linux 9 Essentials. Buy the full book now in eBook or Print format.
Includes 34 chapters and 290 pages. Learn more. |
To use port forwarding, begin by enabling masquerading as follows (in this case, the assumption is made that the interface connected to the internet has been assigned to the external zone):
# firewall-cmd --zone=external --add-masquerade
To forward from a port to a different local port, a command similar to the following would be used:
# firewall-cmd --zone=external --add-forward-port=port=22:proto=tcp:toport=2750
In the above example, any TCP traffic on port 22 will be forwarded to port 2750 on the local system. The following command, on the other hand, forwards port 20 on the local system to port 22 on the system with the IP address 192.168.0.19:
# firewall-cmd --zone=external --add-forward-port=port=20:proto=tcp:toport=22:toaddr=192.168.0.19
Similarly, the following command forwards local port 20 to port 2750 on the system with IP address 192.168.0.18:
# firewall-cmd --zone=external --add-forward-port=port=20:proto=tcp:toport=2750:to addr=192.168.0.18
Managing firewalld from the Cockpit Interface
So far, this chapter has provided an overview of firewalld and explored using the firewall-cmd command-line tool to manage firewall zones and interfaces. While firewall-cmd provides the most flexible way to manage the firewalld configuration, it is also possible to view and manage the services for the default zone within the Cockpit web console.
 |
You are reading a sample chapter from Red Hat Enterprise Linux 9 Essentials. Buy the full book now in eBook or Print format.
Includes 34 chapters and 290 pages. Learn more. |
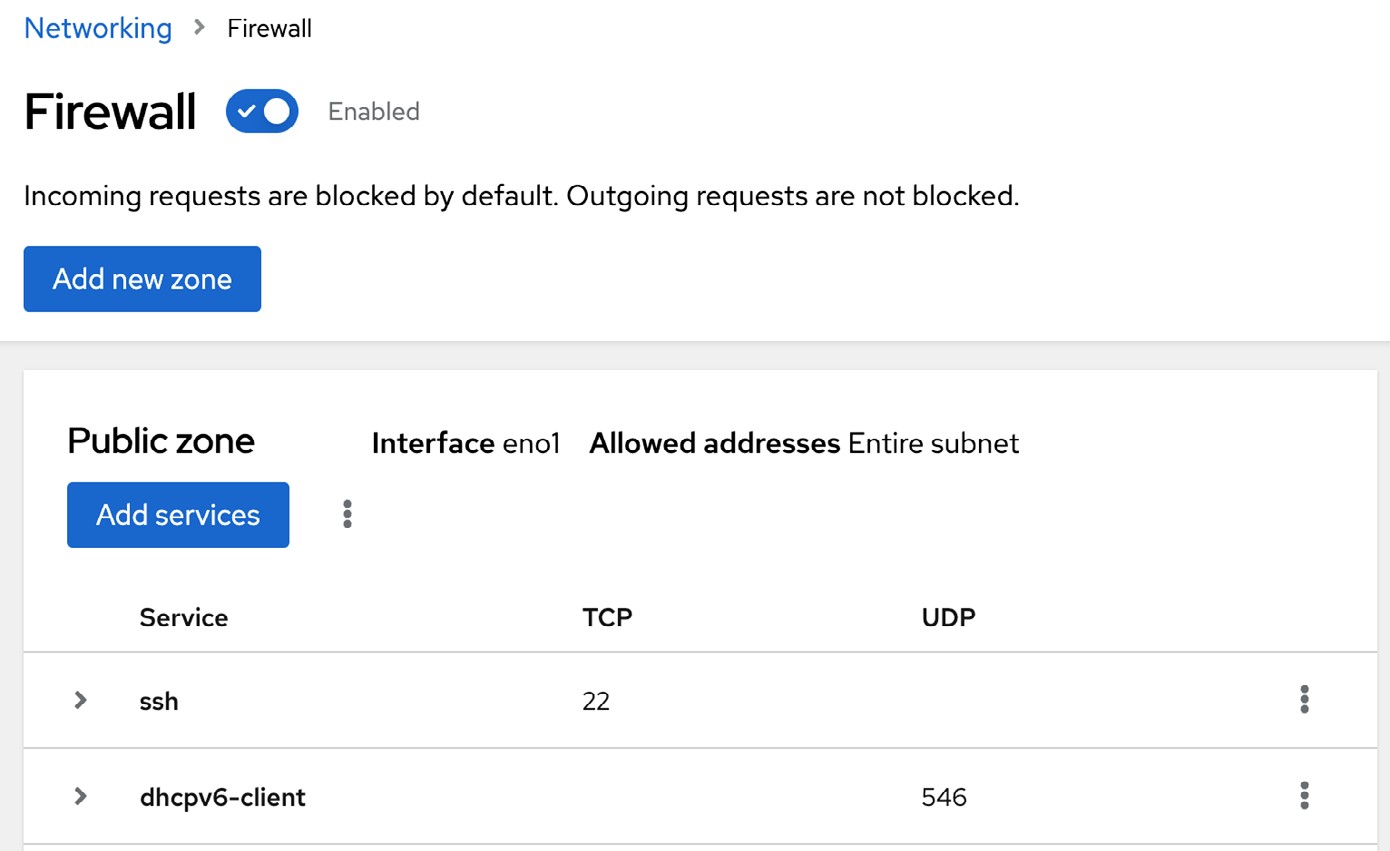
To access the firewalld settings, sign into the Cockpit interface and select Networking from the navigation panel. On the networking page, locate the Firewall section as shown in Figure 14-1 below and click on the Edit rules and zones button:
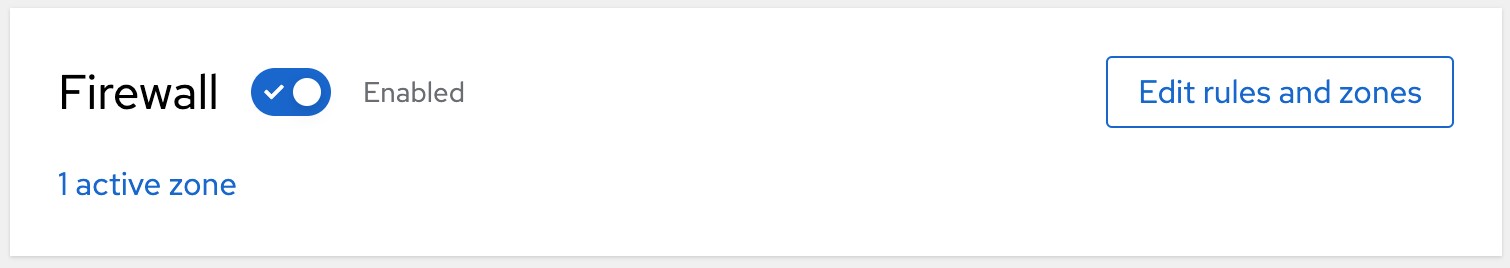
The Firewall page displays the current service rules configured for the default zone (and allows services to be removed using the trash can buttons), new services to be added to the zone, and the firewall to be turned on and off:
Managing firewalld using firewall-config
If you have access to the graphical desktop environment, the firewall may also be configured using the firewall-config tool. Though not installed by default, firewall-config may be installed as follows:
# dnf install firewall-config
When launched, the main firewall-config screen appears as illustrated in Figure 14-1:
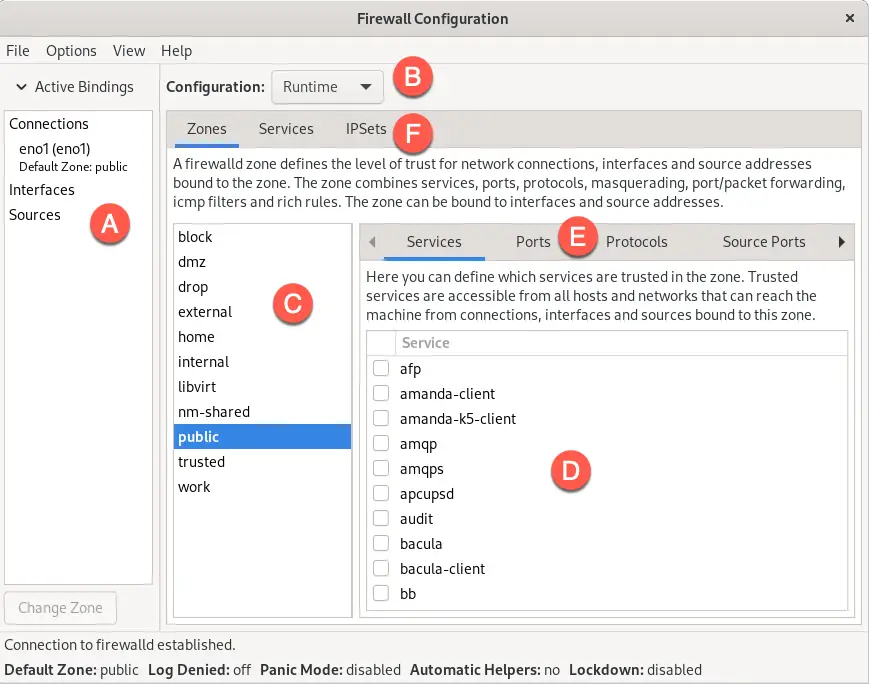
The key areas of the tool can be summarized as follows:
 |
You are reading a sample chapter from Red Hat Enterprise Linux 9 Essentials. Buy the full book now in eBook or Print format.
Includes 34 chapters and 290 pages. Learn more. |
A – Displays all of the currently active interfaces and the zones to which they are assigned. To assign an interface to a different zone, select it from this panel, click the Change Zone button, and select the required zone from the resulting dialog.
B – Controls whether the information displayed and any changes made within the tool apply to the runtime or permanent rules.
C – The list of zones, services, or IPSets configured on the system. The information in this panel depends on the selection made from toolbar F. Selecting an item from the list in this panel updates the main panel marked D.
D – The main panel contains information about the current category selection in toolbar E. In this example, the panel displays services for the public zone. The checkboxes next to each service control whether the service is enabled within the firewall. Within these category panels, new rules can be added or existing rules configured or removed.
E – Controls the content displayed in panel D. Selecting items from this bar shows the current rule for the chosen category.
 |
You are reading a sample chapter from Red Hat Enterprise Linux 9 Essentials. Buy the full book now in eBook or Print format.
Includes 34 chapters and 290 pages. Learn more. |
F – Controls the list displayed in panel C.
The firewall-config tool is straightforward and intuitive to use and allows many of the tasks available with firewall-cmd to be performed in a visual environment.
Summary
A carefully planned and implemented firewall is vital to any secure system. In the case of RHEL 9, the firewalld service provides a firewall system that is both flexible and easy to administer.
The firewalld service uses the concept of zones to group sets of firewall rules and includes a suite of predefined zones designed to meet a range of firewall protection requirements. These zones may be modified to add or remove rules or entirely new zones created and configured. The network devices on the system that connect to networks or the internet are referred to as interfaces. Each interface, in turn, is assigned to a zone. The primary tools for working with firewalld are the firewall-cmd command-line tool and the firewall-config graphical utility. Minimal firewall management options are also available via the Cockpit web interface.